- Google Cloud
- Cloud Forums
- Apigee
- Re: Private key encryption for JWT token generatio...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The jwtgenerate policy is able to generate token if I use the following private key formats.I'm storing the private key in encrypted KVM and referring that variable in the JWT policy
-----BEGIN RSA PRIVATE KEY-----
....
-----END RSA PRIVATE KEY-----
PKCS#8(unencrypted)
-----BEGIN PRIVATE KEY-----
....
-----END PRIVATE KEY-----
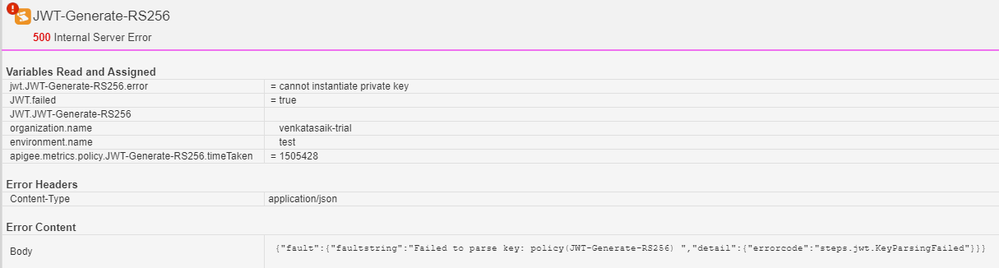
But if I encrypt these keys with passwords and use the encrypted private keys to generate, JWT trace tool shows the following "cannot instantiate private key" error
Encrypted key formats
-----BEGIN RSA PRIVATE KEY-----
Proc-Type: 4, ENCRYPTED
DEK-Info: AES-256-CBC,1E9B7BE131CB1452DA691AF29A321E4D
-----END RSA PRIVATE KEY-----
PKCS#8(encrypted)
-----BEGIN ENCRYPTED PRIVATE KEY-----
....
-----END ENCRYPTED PRIVATE KEY-----
So,
1. Does JWT policy has any preferred format for the PEM encoded private key
2. Why is it failing to parse the encrypted private key?
- Labels:
-
API Runtime
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm not sure why it's failing. Can you show your policy configuration?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
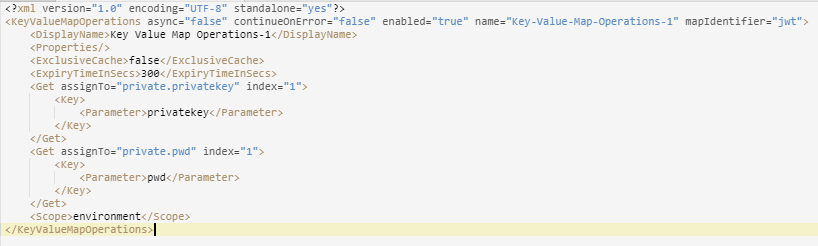
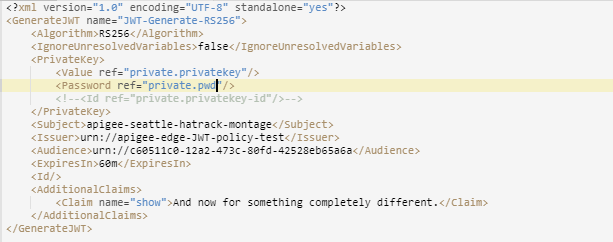
Policy configurations
KVM policy
JWTgenerate
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks, let me look into it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I did as suggested in documentation like getting variables from KVM and providing the correct format but I can't get the exact reason why it is failing.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sorry! See my answer below.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Update: 2019 December 20
Support for alternative encryption algorithms has been added to Apigee.
----------
Regrettably, today the only key encryption algorithm supported is the default "TripleDES", aka des-ede3-cbc.
With openssl, you could generate such a key like this:
openssl genrsa -des3 -out private-encrypted-rsa-des3.pem 2048
If you use a different encryption algorithm, the policy will not successfully read the private key. For example, if you use this command to generate a private key:
openssl genrsa -aes256 -out private-encrypted-rsa-aes256.pem 2048
...then the key will not be parsed successfully by the policy. Similarly, if you use the genpkey command, like this:
openssl genpkey -algorithm RSA -out key.pem -aes-256-cbc -pkeyopt rsa_keygen_bits:4096
..then the key will not be parsed successfully by the policy.
This is an arbitrary limitation in the policy and I've filed a ticket (b/79526748) to request that the limitation be lifted.
The fix is relatively simple, so I would hope we would be able to deliver that pretty quickly, possibly in the next cloud release.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi DIno
I am facing same issue. Is the fix applied
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The fix has been applied but is not yet available in the public cloud. It will deploy to the cloud only later this month. In the meantime you should use the des3 encryption.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am using pvt key given by google api console. So cant change the key
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
ps: here's an article describing how to store these keys in the KVM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Dino,
We are facing the same issue as discussed in the above conversation.
Also we are facing passing the keys in the same format and using the procedure.
Thanks,
Lakshmi Motupalli.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Lakshmi
Can you please ask a new question? Click the button on the upper right labeled "Ask a Question". When you do that, provide as much information as is relevant:
- What version of Apigee are you using?
- What is the specific issue you are facing? Please give details, rather than just saying "same as above". (There are multiple issues that were raised in this 4-year old conversation) What results are you seeing? What results do you expect to see?
- Provide specifics of the configuration you are using. This includes policy configuration, and the details of the JWT you are trying to generate or verify. (mask or remove any private data)
- What other combinations of configuration have you tried? And did the results change?
I'll try to help.
-
Analytics
497 -
API Hub
75 -
API Runtime
11,664 -
API Security
177 -
Apigee General
3,036 -
Apigee X
1,283 -
Developer Portal
1,909 -
Drupal Portal
43 -
Hybrid
463 -
Integrated Developer Portal
89 -
Integration
309 -
PAYG
13 -
Private Cloud Deployment
1,068 -
User Interface
76
| User | Count |
|---|---|
| 1 | |
| 1 | |
| 1 | |
| 1 | |
| 1 |

 Twitter
Twitter