- Google Cloud
- Cloud Forums
- Apigee
- hybrid - missing fine-grain role assignments ( sco...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
With OPDK, platform administrators could explicitly grant permissions to specific proxies - "proxy1" "proxy2" ... etc. This would allow for tight-controls on who is allowed to modify or trace the proxy.
For instance, we have a shared "authentication proxy", which only CIAM/Identity developer have access. No other users should access
Questions
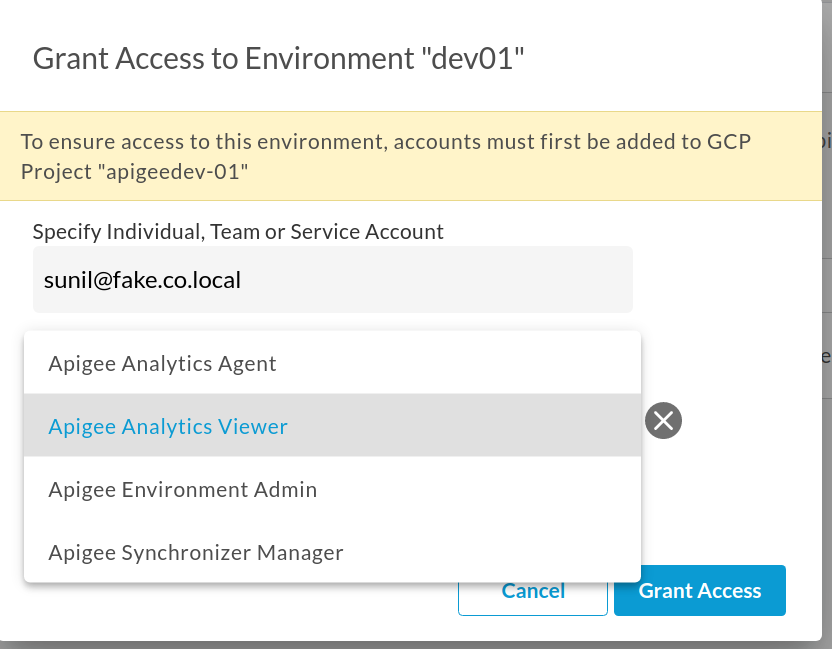
* "Environment access" seems to grant higher-level roles - all or nothing. See image. Doesn't have ability to differentiate between proxy, api product
* GCP-IAM does not provide/allow-for fine-grain restrictions from UI.
* Has anyone tried to create a specific policy at the resource-level ? (product, proxy or entitlement)
- Labels:
-
Hybrid
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In hybrid the capability is there, but it's available differently. You should be able to do this in X or hybrid with Conditional IAM
Read about it here: https://cloud.google.com/apigee/docs/api-platform/system-administration/add-iam-conditions
Let me know if this satisfies your requirement.
-
Analytics
497 -
API Hub
75 -
API Runtime
11,664 -
API Security
177 -
Apigee General
3,036 -
Apigee X
1,283 -
Developer Portal
1,909 -
Drupal Portal
43 -
Hybrid
463 -
Integrated Developer Portal
89 -
Integration
309 -
PAYG
13 -
Private Cloud Deployment
1,068 -
User Interface
76
| User | Count |
|---|---|
| 1 | |
| 1 | |
| 1 | |
| 1 | |
| 1 |

 Twitter
Twitter