- Google Cloud Security
- Google Security Operations
- Articles & Announcements
- Onboarding Journey
- Security Operations SOAR: Step 1 - Configure Integ...
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Article History
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
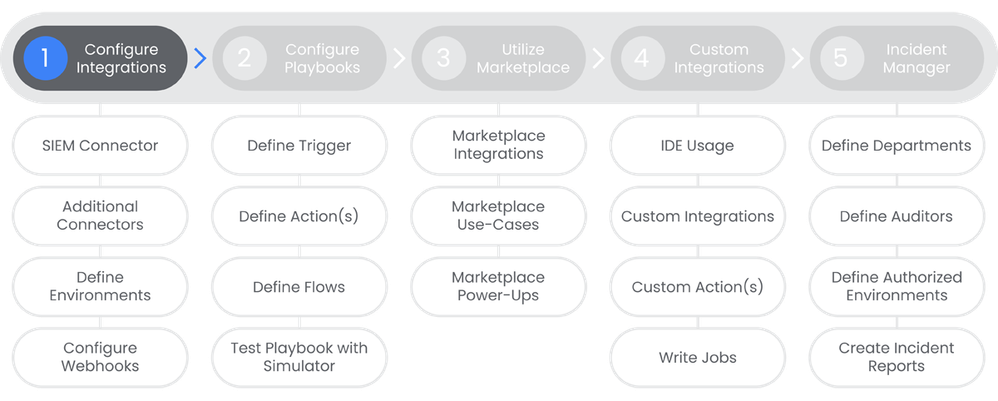
Table of Contents
Below you'll find a table of contents for the Configure Integrations journey.
- Table of Contents
- Prerequisites
- Actions
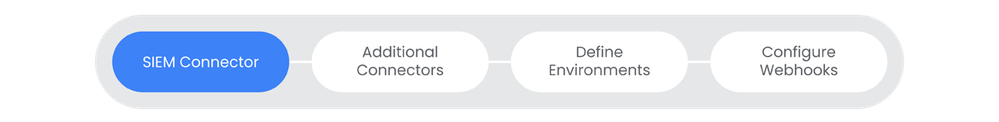
- SIEM Connector
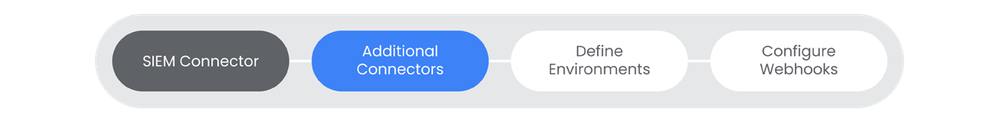
- Additional Connectors
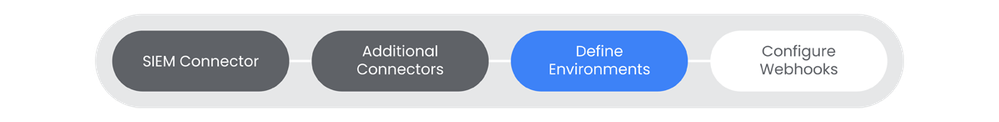
- Define Environments
- Configure Webhooks
SecOps SOAR uses integrations to ingest alerts from a variety of data sources into the platform. A connector is one of the items in an integration package which can be downloaded through the Chronicle Marketplace.
Prerequisites
- Entitlement for Chronicle SOAR on the account and project.
- Administrative permissions to Chronicle SOAR.
- Administrative access for any 3rd party applications that will be integrated with Chronicle SOAR.
Actions
SIEM Connector
Connecting SecOps SIEM and SOAR is a critical step in ensuring that your SOC can take full advantage of the power of SecOps planet scale index and search functionality. This provides SOAR access to the Chronicle UDM.
See the Relevant Links section for more documentation regarding the prerequisites.
- New or existing Chronicle SIEM instance
Steps
-
Note: This connector is setup for the customer automatically by google when SOAR is turned on by the account team.
Relevant Links
Additional Connectors
SecOps SOAR uses connectors to ingest alerts from a variety of data sources. Connectors are Python based applications which pull alerts from 3rd party products parsing and normalizing them for storage in Chronicle's UDM.
Prerequisites
See the Relevant Links section for more documentation regarding the prerequisites.
- New or existing SecOps SIEM instance
- Permissions to add connectors (Read/Write permission for Marketplace, *Allow All)
Steps
-
Navigate to Chronicle Marketplace > Integrations
-
Search for and install Email Integrations
-
Navigate to SOAR Settings > Ingestions > Connectors
-
Select Settings > Configure Default Instance to open the Email Configure Instance dialog box.
-
Fill in all of the required fields (this will vary based on the connector you're configuring)
-
Click Create New Connector
-
Select the IMAP Email Connector, click Create
-
Fill in all of the required fields and click Save. Click Yes on the confirmation dialog.
-
Enable the connector, click Save. This will cause the connector to run periodically to pull in any new emails according to the configuration.
Relevant Links
Define Environments
Environment is simply another word for disparate networks, domains, or customers that are managed by a SOC or MSSP. Environments are useful logical segregation to provide services to different networks, customers or business units within the organization.
Prerequisites
See the Relevant Links section for more documentation regarding the prerequisites.
- New or existing Chronicle SOAR deployment
- Admin access in Chronicle SOAR
Steps
-
In Chronicle SOAR, navigate to Settings > Organization > Environments.
-
Click the "+" icon.
-
Fill out all of the required information, ensuring to click Append to all Users and API Keys if you want to add this new environment directly to existing users and API Keys.
-
Note: Make sure to add an alias if the 3rd party integration has a different tenant name defined.
-
-
Click Create.
Relevant Links
Configure Webhooks
"Webhooks are a lightweight solution for pushing alerts from your organization into the platform. Cases with alerts ingested by webhooks appear in the platform with the same information as cases with alerts ingested using connectors. Note: Crowdstrike is used as an example"
Prerequisites
See the Relevant Links section for more documentation regarding the prerequisites.
- Existing Chronicle SOAR deployment
- Admin access in Chronicle SOAR
Steps
-
Navigate to SOAR Settings > Ingestion > Webhooks.
-
Click Add incoming webhook from the top left.
-
For the sake of this example, we will use Crowdstrike as the 3rd party application.
-
Name the webhook, then click Save.
-
-
Copy the webhook URL, you will need this in your source platform as the webhook destination.
-
Important Note: The webhook is only shown once, copy to a safe location.
-
-
In the Data Mapping section, select Upload JSON sample (use the sample taken from Crowdstrike).
-
Map the Chronicle fields with the corresponding fields in the Crowdstrike JSON data.
-
Once
Detections.Last.Format
appears in the Expression Builder, you can click Run to see the results.

 Twitter
Twitter